Many information security engineer resume submissions fail because they list tools and tasks but skip measurable risk reduction and business impact. That hurts in ATS screening and rapid recruiter scans, where high competition rewards clear outcomes. If you're unsure where to begin, learning how to write a resume that emphasizes results over responsibilities is the first step.
A strong resume shows what you changed and why it mattered. Highlight reduced incident response time, blocked attack paths across key systems, improved audit results, lowered false positives, secured cloud migrations, and delivered controls on schedule.
Key takeaways
- Quantify security outcomes like incident reduction and response time instead of listing routine tasks.
- Use reverse-chronological format for experienced candidates and hybrid format for career changers.
- Tailor every experience bullet to mirror the specific job posting's tools and frameworks.
- Place certifications above education when they're recent and directly relevant to the target role.
- Demonstrate skills through measurable results in your experience section, not just a skills list.
- Enhancv's Bullet Point Generator helps turn vague duties into recruiter-ready, metrics-driven bullets.
- Stop using AI once your resume accurately reflects real experience without inflated claims.
Job market snapshot for information security engineers
We analyzed 148 recent information security engineer job ads across major US job boards. These numbers help you understand career growth patterns, regional hotspots, employer expectations at a glance.
What level of experience employers are looking for information security engineers
| Years of Experience | Percentage found in job ads |
|---|---|
| 1–2 years | 10.1% (15) |
| 3–4 years | 11.5% (17) |
| 5–6 years | 21.6% (32) |
| 7–8 years | 3.4% (5) |
| 9–10 years | 1.4% (2) |
| 10+ years | 2.0% (3) |
| Not specified | 51.4% (76) |
Information security engineer ads by area of specialization (industry)
| Industry (Area) | Percentage found in job ads |
|---|---|
| Finance & Banking | 70.3% (104) |
| Healthcare | 20.3% (30) |
Top companies hiring information security engineers
| Company | Percentage found in job ads |
|---|---|
| Wells Fargo | 29.1% (43) |
| First Horizon Corp. | 10.8% (16) |
Role overview stats
These tables show the most common responsibilities and employment types for information security engineer roles. Use them to align your resume with what employers expect and to understand how the role is structured across the market.
Day-to-day activities and top responsibilities for a information security engineer
| Responsibility | Percentage found in job ads |
|---|---|
| Python | 52.7% (78) |
| Powershell | 41.9% (62) |
| Azure | 30.4% (45) |
| Aws | 25.7% (38) |
| Siem | 23.0% (34) |
| Incident response | 19.6% (29) |
| Information security | 18.2% (27) |
| Bash | 14.9% (22) |
| Cissp | 14.9% (22) |
| Ci/cd | 14.2% (21) |
| Linux | 14.2% (21) |
| Windows | 14.2% (21) |
Type of employment (remote vs on-site vs hybrid)
| Employment type | Percentage found in job ads |
|---|---|
| On-site | 43.9% (65) |
| Hybrid | 41.2% (61) |
| Remote | 14.9% (22) |
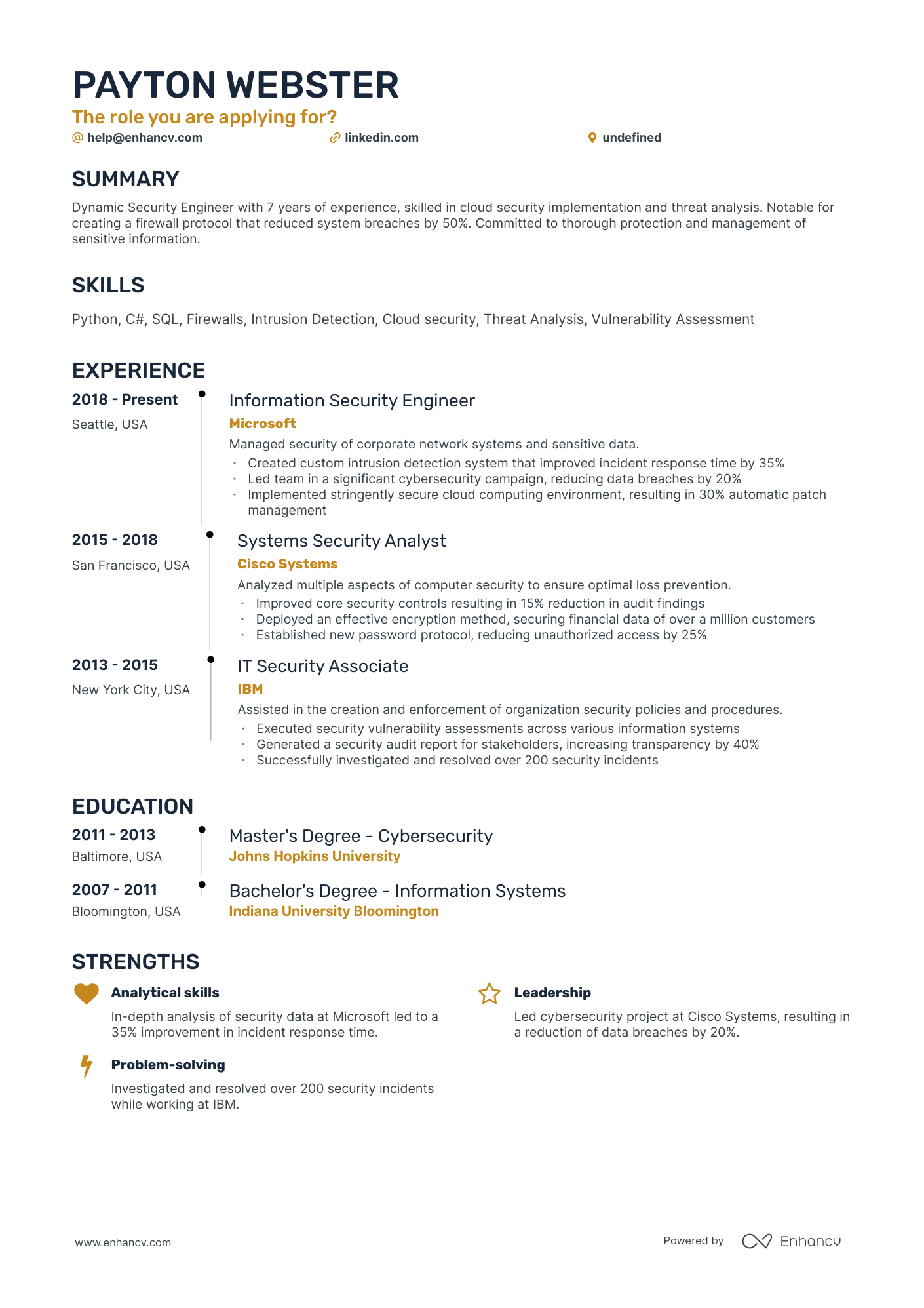
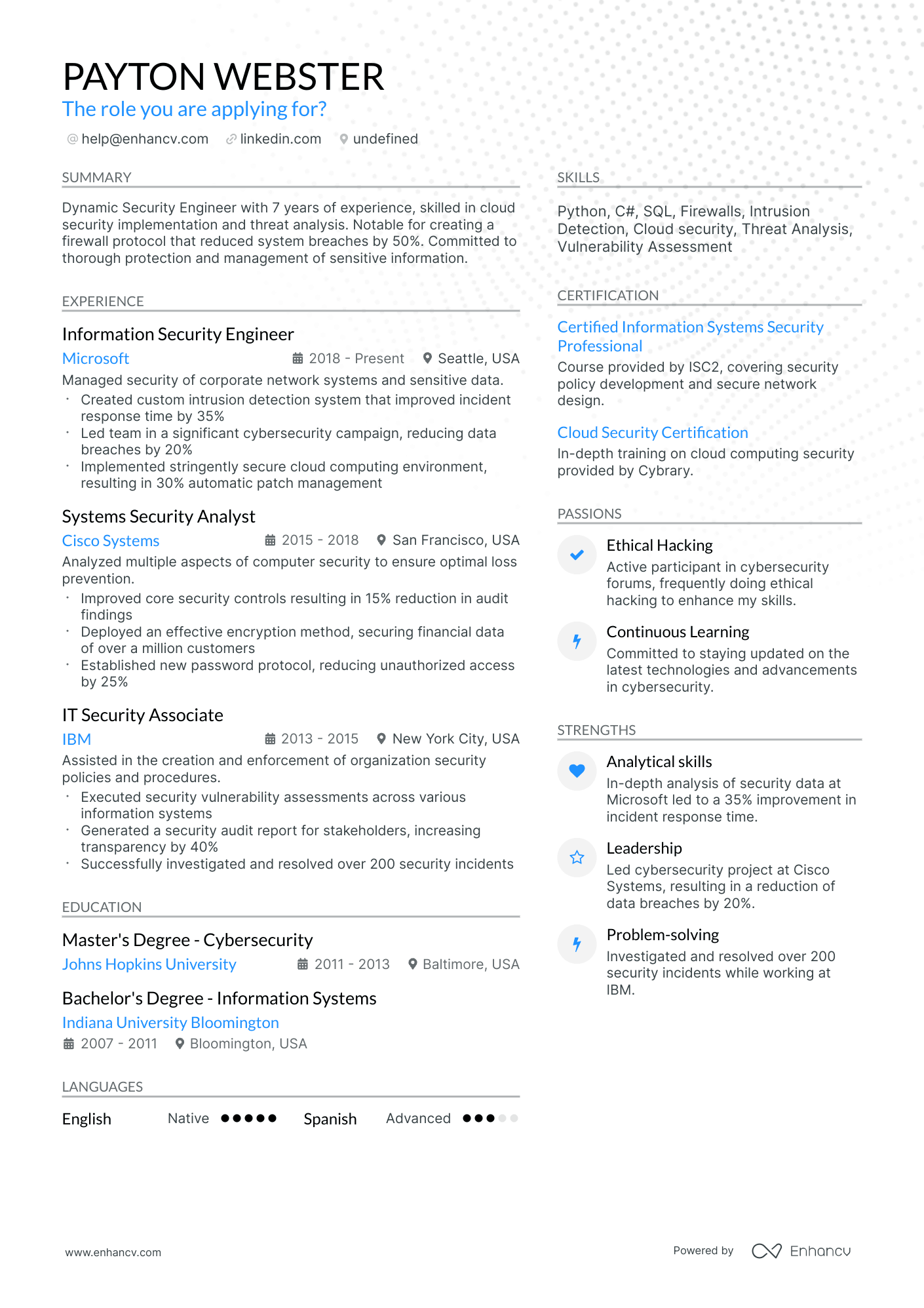
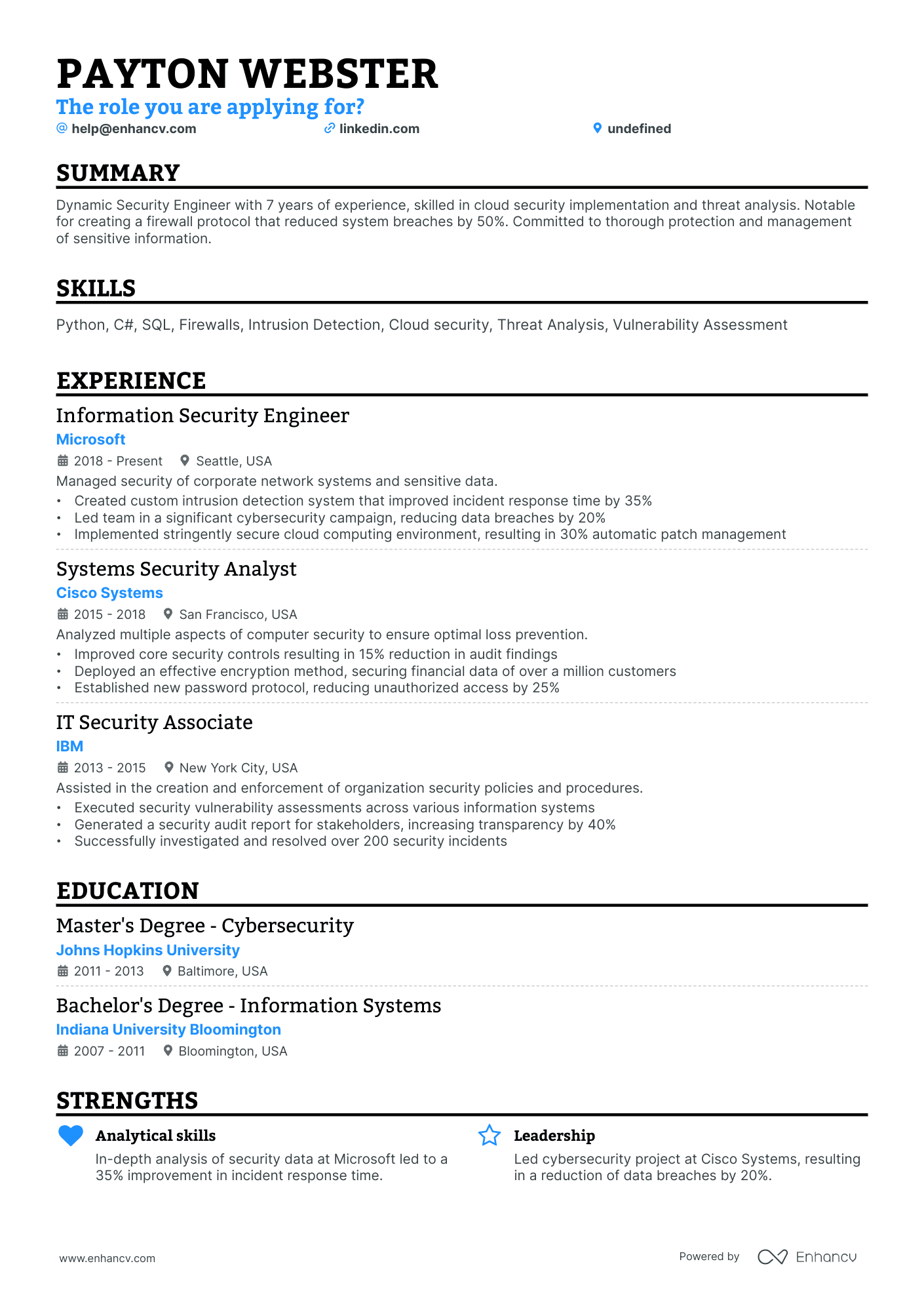
How to format a information security engineer resume
Recruiters evaluating information security engineer candidates prioritize hands-on technical depth across security domains—vulnerability management, network defense, SIEM platforms, and incident response—alongside evidence of risk reduction and compliance outcomes. A clear, well-structured resume format ensures these signals surface quickly during both automated applicant tracking system (ATS) parsing and the recruiter's initial scan.
I have significant experience in this role—which format should I use?
Use a reverse-chronological format to present your security engineering career in a clear, progression-driven timeline. Do:
- Lead each role entry with your scope of ownership: systems protected, team size, environments secured (cloud, on-prem, hybrid), and stakeholder relationships.
- Highlight core tools and domains—SIEM platforms (Splunk, QRadar), IDS/IPS, penetration testing frameworks, cloud security (AWS, Azure), and compliance standards (SOC 2, ISO 27001, NIST).
- Quantify business impact through metrics such as incident reduction rates, mean time to detect/respond improvements, cost savings from automation, or audit pass rates.
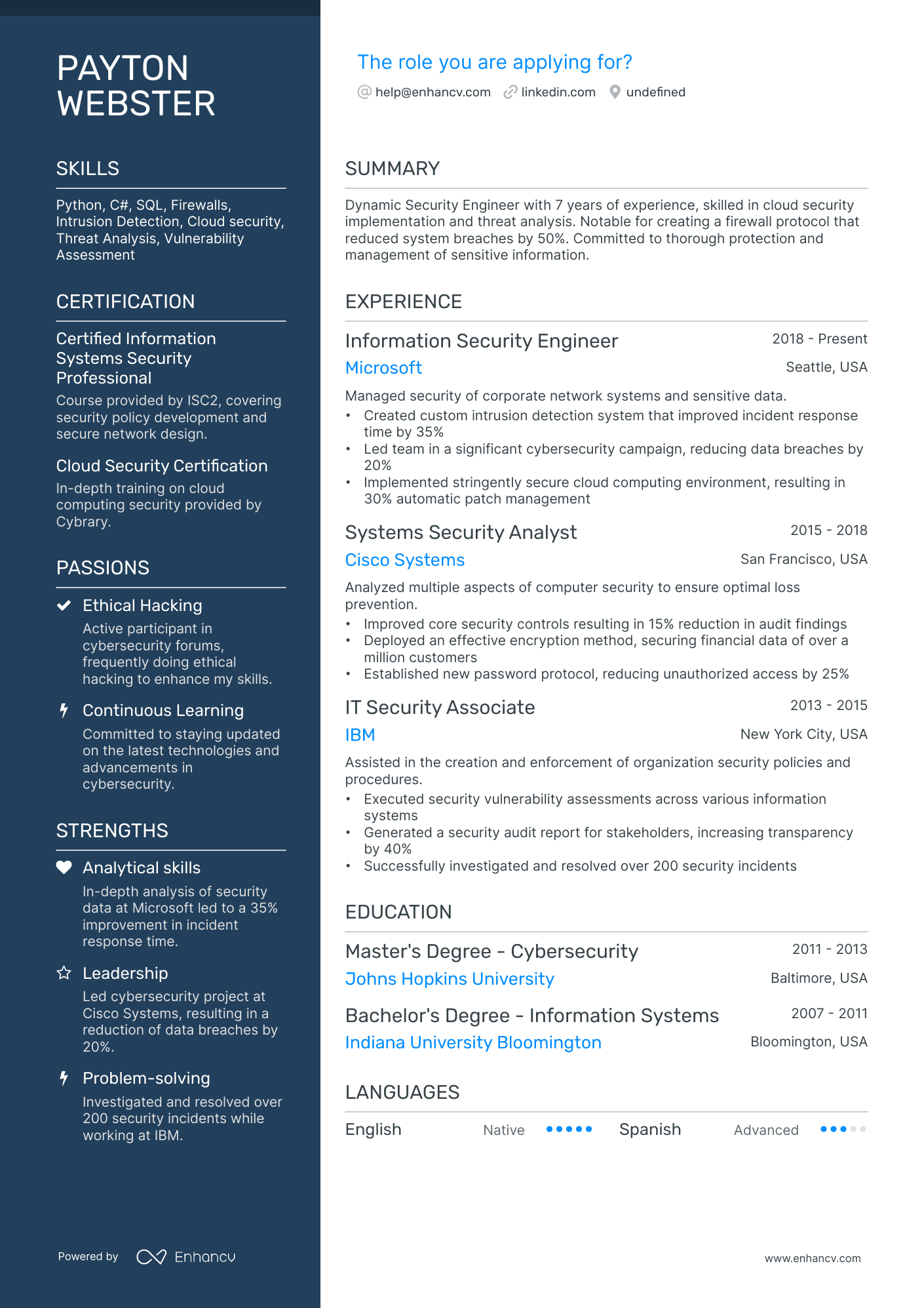
I'm junior or switching into this role—what format works best?
Use a hybrid format that places a focused technical skills section above your experience entries, giving recruiters immediate visibility into your security toolset and certifications. Do:
- Position core competencies—firewalls, vulnerability scanning, endpoint detection, scripting languages (Python, Bash), and relevant certifications (Security+, CEH, GSEC)—in a dedicated skills section near the top of the resume.
- Feature security-related projects, lab environments, CTF competitions, or transitional experience (such as IT support or network administration roles) that demonstrate applied security knowledge.
- Link every action to a measurable or observable result so recruiters can assess your readiness for a dedicated security engineering seat.
Why not use a functional resume?
A functional format strips away the timeline context recruiters need to verify where and how you applied your security skills, making it difficult to assess growth, tool exposure, and real-world accountability. A functional resume may be acceptable if you're transitioning from a related field (network engineering, systems administration, or software development) with no dedicated security job titles yet—but only if you anchor every listed skill to a specific project, lab, or outcome rather than presenting skills in isolation.
With your format set, the next step is filling it with the right sections to highlight your information security expertise.
What sections should go on a information security engineer resume
Recruiters expect you to present clear evidence that you can protect systems, reduce risk, and respond to threats in production environments. Knowing what to put on a resume for a security role helps you prioritize the right details. Use this structure for maximum clarity:
- Header
- Summary
- Experience
- Skills
- Projects
- Education
- Certifications
- Optional sections: Awards, Publications, Open-source work
Strong experience bullets should emphasize measurable security impact, incident and risk outcomes, environment scope, and results delivered across stakeholders.
Is your resume good enough?
Drop your resume here or choose a file. PDF & DOCX only. Max 2MB file size.
Once you’ve organized your resume with the right core components, the next step is to write your information security engineer experience section so those sections clearly show your impact and fit.
How to write your information security engineer resume experience
Your experience section should highlight the security initiatives you've shipped, the tools and methodologies you've applied, and the measurable outcomes you've achieved in protecting organizational assets. Hiring managers prioritize demonstrated impact—such as reduced vulnerabilities, faster incident response, or strengthened compliance posture—over descriptive task lists. Building a targeted resume that aligns each bullet with the role's requirements makes your experience section far more compelling.
Each entry should include:
- Job title
- Company and location (or remote)
- Dates of employment (month and year)
Three to five concise bullet points showing what you owned, how you executed, and what outcomes you delivered:
- Ownership scope: the security infrastructure, network environments, cloud platforms, applications, or compliance programs you were directly accountable for maintaining and hardening.
- Execution approach: the frameworks, technologies, and methods you relied on—such as SIEM platforms, intrusion detection systems, vulnerability scanners, penetration testing methodologies, or zero-trust architecture principles—to identify threats, enforce policies, and deliver secure solutions.
- Value improved: the specific dimensions of security posture you strengthened, whether that involved reducing mean time to detect or respond, decreasing the attack surface, improving patch management efficiency, elevating compliance readiness, or lowering organizational risk exposure.
- Collaboration context: how you partnered with engineering teams, DevOps, IT operations, compliance officers, executive leadership, or third-party auditors to embed security practices across the organization and align defenses with business objectives.
- Impact delivered: the tangible outcomes your work produced, expressed through risk reduction, incident containment results, audit findings resolved, security program maturity gains, or business continuity improvements rather than routine activity descriptions.
Experience bullet formula
A information security engineer experience example
✅ Right example - modern, quantified, specific.
Information Security Engineer
Northbridge Health | Remote
2022–Present
Digital health platform supporting 3M+ patient accounts across web and mobile, operating in a regulated (HIPAA) environment.
- Implemented AWS IAM Identity Center, least-privilege IAM roles, and Terraform guardrails; cut overprivileged permissions by 62% and reduced access provisioning time from two days to two hours.
- Built a SIEM pipeline using Splunk, AWS CloudTrail, and VPC Flow Logs with MITRE ATT&CK-aligned detections; reduced mean time to detect from eight hours to forty-five minutes and lowered false positives by 28%.
- Led vulnerability management across container and cloud workloads using Wiz, Trivy, and Snyk; partnered with platform engineers to remediate 1,100+ findings and reduced critical vulnerabilities by 71% in two quarters.
- Hardened Kubernetes and CI/CD security with OPA Gatekeeper, Kubernetes NetworkPolicies, and GitHub Actions secret scanning; prevented twelve policy-violating deployments per month and eliminated plaintext secret leaks in builds.
- Coordinated incident response with engineering, legal, and customer success using PagerDuty and Jira; contained three high-severity incidents within one hour and improved post-incident action closure rate from 64% to 92%.
Now that you've seen how a strong experience section comes together, let's look at how to adjust yours to match the specific job you're targeting.
How to tailor your information security engineer resume experience
Recruiters evaluate your information security engineer resume through both applicant tracking systems and manual review. Tailoring your resume to the job description ensures your qualifications stand out in both rounds.
Ways to tailor your information security engineer experience:
- Match specific SIEM platforms and security tools named in the posting.
- Mirror the compliance frameworks listed such as NIST ISO or SOC.
- Use the exact vulnerability management terminology the employer references.
- Highlight incident response workflows that align with their described processes.
- Emphasize cloud security experience when the role specifies AWS Azure or GCP.
- Include penetration testing or threat modeling methods the posting prioritizes.
- Reference zero trust architecture experience if the job description mentions it.
- Align your metrics with the KPIs or success criteria they outline.
Tailoring means aligning your real accomplishments with what the employer asks for, not forcing keywords where they don't belong.
Resume tailoring examples for information security engineer
| Job description excerpt | Untailored | Tailored |
|---|---|---|
| "Manage SIEM platform (Splunk) to detect and respond to threats across hybrid cloud environments, including AWS and Azure infrastructure." | Monitored security systems and responded to incidents as needed. | Managed Splunk SIEM platform to detect and respond to threats across hybrid AWS and Azure environments, tuning correlation rules that reduced false positives by 37% and cut mean time to detection from 45 minutes to 12 minutes. |
| "Conduct vulnerability assessments and penetration testing using Nessus and Burp Suite, and drive remediation efforts with development teams within SLA timelines." | Performed security testing and helped fix vulnerabilities found during scans. | Conducted vulnerability assessments and penetration tests using Nessus and Burp Suite across 200+ assets, collaborating directly with development teams to drive remediation of critical findings within 72-hour SLA timelines. |
| "Design and enforce zero trust architecture policies, implement identity and access management controls using Okta, and ensure compliance with NIST 800-53 and SOC 2 frameworks." | Worked on access control policies and helped maintain compliance with security standards. | Designed and enforced zero trust architecture policies for a 3,000-user organization, implementing Okta-based identity and access management controls and maintaining continuous compliance with NIST 800-53 and SOC 2 frameworks across four annual audit cycles. |
Once your experience aligns with the specific security role’s requirements, the next step is to quantify your information security engineer achievements to show the measurable impact of that work.
How to quantify your information security engineer achievements
Quantifying your achievements proves you reduced risk and improved reliability, not just stayed busy. Focus on incident reduction, detection and response time, vulnerability closure rates, control coverage, and security-driven cost savings.
Quantifying examples for information security engineer
| Metric | Example |
|---|---|
| Incident reduction | "Cut phishing-related account takeovers by 42% in six months by tuning Microsoft Defender for Office 365 policies and enforcing conditional access." |
| Detection speed | "Reduced mean time to detect from 55 minutes to 12 minutes by onboarding 120 log sources into Splunk and creating eight high-fidelity correlation rules." |
| Response time | "Lowered mean time to respond from 4.1 hours to 1.6 hours by automating triage with Cortex XSOAR playbooks for malware and suspicious login alerts." |
| Vulnerability closure | "Improved critical vulnerability remediation within 14 days from 63% to 91% across 300 servers by integrating Tenable scans with Jira workflows." |
| Cost avoidance | "Avoided $180,000 in annual spend by consolidating endpoint agents from three tools to CrowdStrike and retiring redundant licenses across 2,400 devices." |
Turn vague job duties into measurable, recruiter-ready resume bullets in seconds with Enhancv's Bullet Point Generator.
Once you've crafted strong bullet points for your experience section, the next step is ensuring your resume also highlights the right hard and soft skills that information security engineer roles demand.
How to list your hard and soft skills on a information security engineer resume
Your skills section shows how you secure systems end-to-end, and recruiters and ATS scan this section for role-matched keywords, so aim for a balanced mix of hard skills and job-specific soft skills that support incident response and risk reduction. information security engineer roles require a blend of:
- Product strategy and discovery skills.
- Data, analytics, and experimentation skills.
- Delivery, execution, and go-to-market discipline.
- Soft skills.
Your skills section should be:
- Scannable (bullet-style grouping).
- Relevant to the job post.
- Backed by proof in experience bullets.
- Updated with current tools.
Place your skills section:
- Above experience if you're junior or switching careers.
- Below experience if you're mid/senior with strong achievements.
Hard skills
- SIEM: Splunk, Microsoft Sentinel
- EDR: CrowdStrike, Microsoft Defender
- Cloud security: AWS, Azure, Google Cloud
- Identity and access management, single sign-on
- Privileged access management
- Vulnerability management: Tenable, Qualys
- Threat modeling: STRIDE
- Application security testing: SAST, DAST
- Security automation: Python, PowerShell
- Infrastructure as code security: Terraform
- Incident response, digital forensics
- NIST Cybersecurity Framework, ISO 27001
Soft skills
- Write clear incident reports
- Triage alerts under pressure
- Lead blameless post-incident reviews
- Translate risk for nontechnical partners
- Challenge requirements with evidence
- Align security controls with business goals
- Drive remediation with owners and deadlines
- Negotiate secure-by-default solutions
- Coordinate across engineering and IT
- Communicate trade-offs and impact
- Maintain strong operational ownership
- Document decisions and runbooks consistently
How to show your information security engineer skills in context
Skills shouldn't live only in a dedicated skills list. You can explore common resume skills to ensure you're not overlooking capabilities that match your target role.
They should be demonstrated in:
- Your summary (high-level professional identity)
- Your experience (proof through outcomes)
Here's what strong, skill-rich entries look like in practice.
Summary example
Senior information security engineer with 10+ years protecting cloud-native financial platforms. Skilled in SIEM architecture, zero-trust frameworks, and incident response. Led threat detection overhaul using Splunk and CrowdStrike, reducing mean time to containment by 62%.
- Reflects senior-level depth immediately
- Names industry-relevant tools explicitly
- Quantifies a meaningful security outcome
- Signals leadership and cross-team collaboration
Experience example
Information Security Engineer
Ridgeline Federal Solutions | Remote
March 2021–Present
- Deployed Palo Alto Cortex XDR across 14 business units with IT and DevOps teams, cutting endpoint incident volume by 41%.
- Designed automated vulnerability scanning pipelines using Tenable.io, reducing patch remediation cycles from 30 days to nine.
- Partnered with compliance analysts to implement NIST 800-53 controls, achieving FedRAMP authorization three months ahead of schedule.
- Every bullet includes measurable proof
- Skills surface naturally through real outcomes
Once you’ve demonstrated your information security engineer skills through relevant projects and outcomes, the next step is to apply the same approach to a resume when you have no experience, so you can present your capabilities clearly and credibly.
How do I write a information security engineer resume with no experience
Even without full-time experience, you can demonstrate readiness through:
- Home lab Active Directory hardening
- Capture the Flag competitions results
- Open-source security tool contributions
- Bug bounty reports and writeups
- Internship or co-op security tasks
- Security coursework with lab reports
- Personal SIEM log analysis projects
- Cloud security sandbox configurations
Our guide on writing a resume without work experience covers additional strategies for showcasing your capabilities when you lack formal job titles.
Focus on:
- Incident detection and triage evidence
- Vulnerability assessment and remediation results
- Security tooling across environments
- Clear, measurable security outcomes
Resume format tip for entry-level information security engineer
Use a hybrid resume format because it highlights skills and projects first, while still showing steady education, labs, and any related work history. Do:
- Put a "Projects" section above work history.
- List tools used for each project.
- Quantify results with counts or percentages.
- Map bullets to job posting requirements.
- Include a technical skills section.
- Built a Splunk SIEM home lab, onboarded three Windows log sources, and reduced suspicious PowerShell false positives by 35% using tuned detection rules.
Since your education section carries extra weight when you lack professional experience, presenting it strategically can help demonstrate your foundational knowledge and relevant qualifications.
How to list your education on a information security engineer resume
Your education section helps hiring teams confirm you have the foundational technical knowledge an information security engineer needs. It validates your training in key areas fast.
Include:
- Degree name
- Institution
- Location
- Graduation year
- Relevant coursework (for juniors or entry-level candidates)
- Honors & GPA (if 3.5 or higher)
Skip month and day details—list the graduation year only.
Here's a strong education entry tailored for an information security engineer resume:
Example education entry
Bachelor of Science in Cybersecurity
George Mason University, Fairfax, VA
Graduated 2021
GPA: 3.7/4.0
- Relevant Coursework: Network Defense, Cryptography, Ethical Hacking, Security Architecture, Digital Forensics
- Honors: Magna Cum Laude, Dean's List (six semesters)
How to list your certifications on a information security engineer resume
Listing certifications on your resume shows an information security engineer's commitment to continuous learning, hands-on tool proficiency, and alignment with current industry standards and frameworks.
Include:
- Certificate name
- Issuing organization
- Year
- Optional: credential ID or URL
- Place certifications below education when your degree is recent and your certifications are older or less relevant to the target information security engineer role.
- Place certifications above education when they're recent, highly relevant, or required for the information security engineer role you're targeting.
Best certifications for your information security engineer resume
- Certified Information Systems Security Professional (CISSP)
- Certified Information Security Manager (CISM)
- CompTIA Security+
- GIAC Security Essentials (GSEC)
- Certified Ethical Hacker (CEH)
- Offensive Security Certified Professional (OSCP)
- AWS Certified Security – Specialty
Once you’ve positioned your credentials to validate your security expertise, shift to your resume summary to highlight that value upfront for hiring managers.
How to write your information security engineer resume summary
Your resume summary is the first thing a recruiter reads. A strong one immediately signals you have the right skills and experience for an information security engineer role.
Keep it to three to four lines, with:
- Your title and relevant years of experience in information security.
- The domain or industry you've worked in, such as cloud security or financial services.
- Core tools and technologies like SIEM platforms, firewalls, IDS/IPS, or vulnerability scanners.
- One or two quantified achievements that show your impact.
- Soft skills tied to real outcomes, such as cross-team collaboration that improved incident response times.
PRO TIP
At this level, focus on technical proficiency, relevant certifications, and early wins that prove you can deliver. Highlight specific tools you've used and problems you've solved. Avoid vague phrases like "passionate self-starter" or "eager to learn." Recruiters want evidence, not enthusiasm.
Example summary for a information security engineer
Information security engineer with three years of experience in cloud and network security. Reduced vulnerability remediation time by 35% using Splunk and Qualys across AWS environments. Skilled in firewall management, incident response, and cross-functional security awareness training.
Optimize your resume summary and objective for ATS
Drop your resume here or choose a file.
PDF & DOCX only. Max 2MB file size.
Now that your summary captures your security expertise at a glance, make sure your header provides the essential contact details recruiters need to actually reach you.
What to include in a information security engineer resume header
A resume header lists your key identifiers and contact details, boosting visibility, credibility, and recruiter screening for a information security engineer role.
Essential resume header elements
- Full name
- Tailored job title and headline
- Location
- Phone number
- Professional email
- GitHub link
- Portfolio link
A LinkedIn link helps recruiters verify experience quickly and supports screening.
Do not include photos on a information security engineer resume unless the role is explicitly front-facing or appearance-dependent.
Use a clear headline with your core security focus and keep links short, working, and consistent across profiles.
Example
Information security engineer resume header
Jordan Lee
Information Security Engineer | Incident Response and Cloud Security
Austin, TX
(512) 555-01XX
jordan.lee@enhancv.com
github.com/jordanlee
jordanlee.com
linkedin.com/in/jordanlee
Once your resume header clearly identifies you and your security credentials, add additional sections to reinforce your qualifications and relevance.
Additional sections for information security engineer resumes
When your core qualifications match other candidates, additional sections can set you apart and reinforce your credibility as an information security engineer.
- Security certifications and clearances
- Publications and threat research
- Conference presentations and speaking engagements
- Open-source security tool contributions
- Languages
- Professional memberships and affiliations
- Capture the Flag (CTF) competitions and awards
Once you've strengthened your resume with relevant additional sections, pairing it with a tailored cover letter can further set your application apart.
Do information security engineer resumes need a cover letter
A cover letter isn't required for an information security engineer, but it helps in competitive searches or when hiring managers expect one. If you're wondering what a cover letter is and when it adds value, consider using one when your resume needs context or when several candidates look similar on paper.
Use a cover letter when it adds clarity and proof:
- Explain role or team fit by mapping your strengths to the job's threat model, tooling, and collaboration style with engineering and product.
- Highlight one or two relevant projects or outcomes, including scope, your role, and measurable impact on risk, uptime, or incident response time.
- Show understanding of the product, users, and business context by naming key assets, likely abuse cases, and pragmatic controls that won't block delivery.
- Address career transitions or non-obvious experience by connecting past work to security outcomes, such as secure design reviews, automation, or audit readiness.
Drop your resume here or choose a file.
PDF & DOCX only. Max 2MB file size.
Even if you decide a cover letter isn’t necessary for every application, using AI to improve your information security engineer resume helps you strengthen the document hiring teams will review first.
Using AI to improve your information security engineer resume
AI can sharpen your resume's clarity, structure, and impact. It helps refine bullet points and align content with information security engineer roles. If you're curious about which AI is best for writing resumes, the answer depends on your needs—but overuse kills authenticity. Once your resume reads clearly and fits the role, step away from AI.
Here are 10 practical prompts to strengthen specific sections of your information security engineer resume:
Strengthen your summary
Quantify experience bullets
Align skills section
Tighten project descriptions
Improve action verbs
Tailor to job posting
Refine certifications section
Clarify education details
Remove redundant content
Check role-specific language
Conclusion
A strong information security engineer resume proves impact with measurable outcomes, such as reduced incidents, faster response times, and improved audit results. It highlights role-specific skills, including threat detection, incident response, vulnerability management, and security tooling, with clear, consistent structure.
Keep each section easy to scan, and connect your work to business risk and reliability. This approach shows you can meet today’s hiring standards and adapt to near-future security needs.