Many application security engineer resume drafts fail because they list tools and generic duties, not risk reduction or delivery impact. That blurs your value in ATS screening, rapid recruiter scans, and a crowded market.
A strong resume shows how you improved security outcomes and enabled shipping safely. Understanding how to make your resume stand out starts with highlighting vulnerabilities eliminated, high-risk findings reduced, mean time to remediate improved, secure releases delivered, and incidents prevented. Quantify scope across applications, teams, and pipelines.
Key takeaways
- Quantify security outcomes like vulnerabilities reduced and remediation time improved in every experience bullet.
- Use reverse-chronological format if experienced and hybrid format if junior or switching careers.
- Tailor your resume to each job posting by mirroring its exact tools, frameworks, and terminology.
- Demonstrate skills in context through your summary and experience, not just in a skills list.
- Anchor entry-level resumes in projects like bug bounties, CTF challenges, and OWASP lab work.
- Place certifications above education when they're recent and directly relevant to the target role.
- Build and refine your application security engineer resume with Enhancv to align structure and content faster.
Job market snapshot for application security engineers
We analyzed 145 recent application security engineer job ads across major US job boards. These numbers help you understand employer expectations, industry demand, salary landscape at a glance.
What level of experience employers are looking for application security engineers
| Years of Experience | Percentage found in job ads |
|---|---|
| 1–2 years | 0.7% (1) |
| 3–4 years | 6.2% (9) |
| 5–6 years | 15.2% (22) |
| 7–8 years | 33.8% (49) |
| 9–10 years | 3.4% (5) |
| 10+ years | 3.4% (5) |
| Not specified | 40.7% (59) |
Application security engineer ads by area of specialization (industry)
| Industry (Area) | Percentage found in job ads |
|---|---|
| Finance & Banking | 44.1% (64) |
| Healthcare | 38.6% (56) |
| Education | 9.7% (14) |
Top companies hiring application security engineers
| Company | Percentage found in job ads |
|---|---|
| CVS Health | 28.3% (41) |
| State Street Corporation | 8.3% (12) |
Role overview stats
These tables show the most common responsibilities and employment types for application security engineer roles. Use them to align your resume with what employers expect and to understand how the role is structured across the market.
Day-to-day activities and top responsibilities for a application security engineer
| Responsibility | Percentage found in job ads |
|---|---|
| Python | 72.4% (105) |
| Aws | 65.5% (95) |
| Java | 55.9% (81) |
| Azure | 54.5% (79) |
| Javascript | 52.4% (76) |
| Kubernetes | 48.3% (70) |
| Gcp | 43.4% (63) |
| Application security | 40.7% (59) |
| Powershell | 37.2% (54) |
| Sast | 35.9% (52) |
| Pci | 35.2% (51) |
| Ci/cd | 34.5% (50) |
Type of employment (remote vs on-site vs hybrid)
| Employment type | Percentage found in job ads |
|---|---|
| On-site | 69.0% (100) |
| Hybrid | 17.9% (26) |
| Remote | 13.1% (19) |
How to format a application security engineer resume
Recruiters evaluating application security engineers prioritize hands-on expertise in secure code review, threat modeling, and vulnerability remediation, along with clear evidence of cross-functional collaboration with development teams. Choosing the right resume format determines how quickly these signals surface during the six to ten seconds a hiring manager spends on an initial scan and whether an applicant tracking system (ATS) can parse your experience correctly.
I have significant experience in this role—which format should I use?
Use a reverse-chronological format—it's the strongest choice for experienced application security engineers because it foregrounds your progression across increasingly complex security programs. Do:
- Lead each role entry with scope and ownership details: number of applications secured, size of engineering teams supported, and reporting structure.
- Highlight domain-specific tools and competencies—static application security testing (SAST), dynamic application security testing (DAST), software composition analysis, threat modeling frameworks, and secure SDLC integration.
- Quantify outcomes tied to business impact, such as reduction in critical vulnerabilities, faster remediation cycles, or compliance milestones achieved.
I'm junior or switching into this role—what format works best?
A hybrid format works best because it lets you lead with relevant security skills and certifications while still showing a timeline of practical experience. Do:
- Place a dedicated skills section near the top featuring application security tools (Burp Suite, Checkmarx, SonarQube), programming languages, and frameworks you've worked with.
- Include project-based entries—capture-the-flag competitions, bug bounty contributions, secure code review exercises, or open-source security audits—to demonstrate applied knowledge.
- Link every action to a measurable or observable result so recruiters can assess your impact even without years of tenure.
Why not use a functional resume?
A functional resume strips away the timeline context that hiring managers need to verify where, when, and how you applied your application security skills, making it harder to assess real-world competency and easier for an ATS to misinterpret your experience. Avoid this format entirely unless you have no other way to present your qualifications coherently.
- A functional format may be acceptable if you're transitioning from a related role (penetration tester, software developer, or systems administrator) with no direct application security job titles, or if you have significant resume gaps—but only if every listed skill is anchored to a specific project, engagement, or measurable outcome.
Once you've established a clean, readable format, the next step is deciding which sections to include so each one strengthens your candidacy.
What sections should go on a application security engineer resume
Recruiters expect to see clear evidence that you can secure applications across the software development lifecycle and reduce risk through measurable improvements. Knowing what to put on a resume for this role is critical to passing both ATS screening and manual review.
Use this structure for maximum clarity:
- Header
- Summary
- Experience
- Skills
- Projects
- Education
- Certifications
- Optional sections: Publications, Open-source work, Leadership
Strong experience bullets should emphasize security impact, quantified outcomes, scope across teams and systems, and results such as vulnerabilities prevented, remediation time reduced, and secure release velocity improved.
Is your resume good enough?
Drop your resume here or choose a file. PDF & DOCX only. Max 2MB file size.
Once you’ve organized your resume with the right core components, the next step is to write your application security engineer experience in a way that fits that structure and shows your impact.
How to write your application security engineer resume experience
The experience section is where you prove you've shipped meaningful security improvements—through threat modeling, secure code reviews, vulnerability remediation, and tooling you directly implemented or managed. Hiring managers prioritize demonstrated impact over descriptive task lists, so every bullet should connect your work to a measurable outcome like reduced vulnerabilities, faster remediation cycles, or strengthened application defenses. Building a targeted resume ensures each entry reflects what the specific employer values most.
Each entry should include:
- Job title
- Company and location (or remote)
- Dates of employment (month and year)
Three to five concise bullet points showing what you owned, how you executed, and what outcomes you delivered:
- Ownership scope: the applications, services, codebases, or security programs you were directly accountable for, including the scale of systems, teams, or environments under your purview as an application security engineer.
- Execution approach: the static and dynamic analysis tools, penetration testing frameworks, secure development lifecycle practices, or threat modeling methodologies you used to identify vulnerabilities and drive remediation.
- Value improved: the specific gains in security posture, code quality, remediation speed, compliance readiness, or risk reduction your work produced across the applications you protected.
- Collaboration context: how you partnered with software engineering, DevOps, product, or compliance teams to embed security into development workflows, triage findings, and align on prioritized fixes.
- Impact delivered: the concrete results your efforts produced—expressed through reduction in attack surface, faster mean time to remediate, improved audit outcomes, or strengthened resilience—rather than a list of tasks you performed.
Experience bullet formula
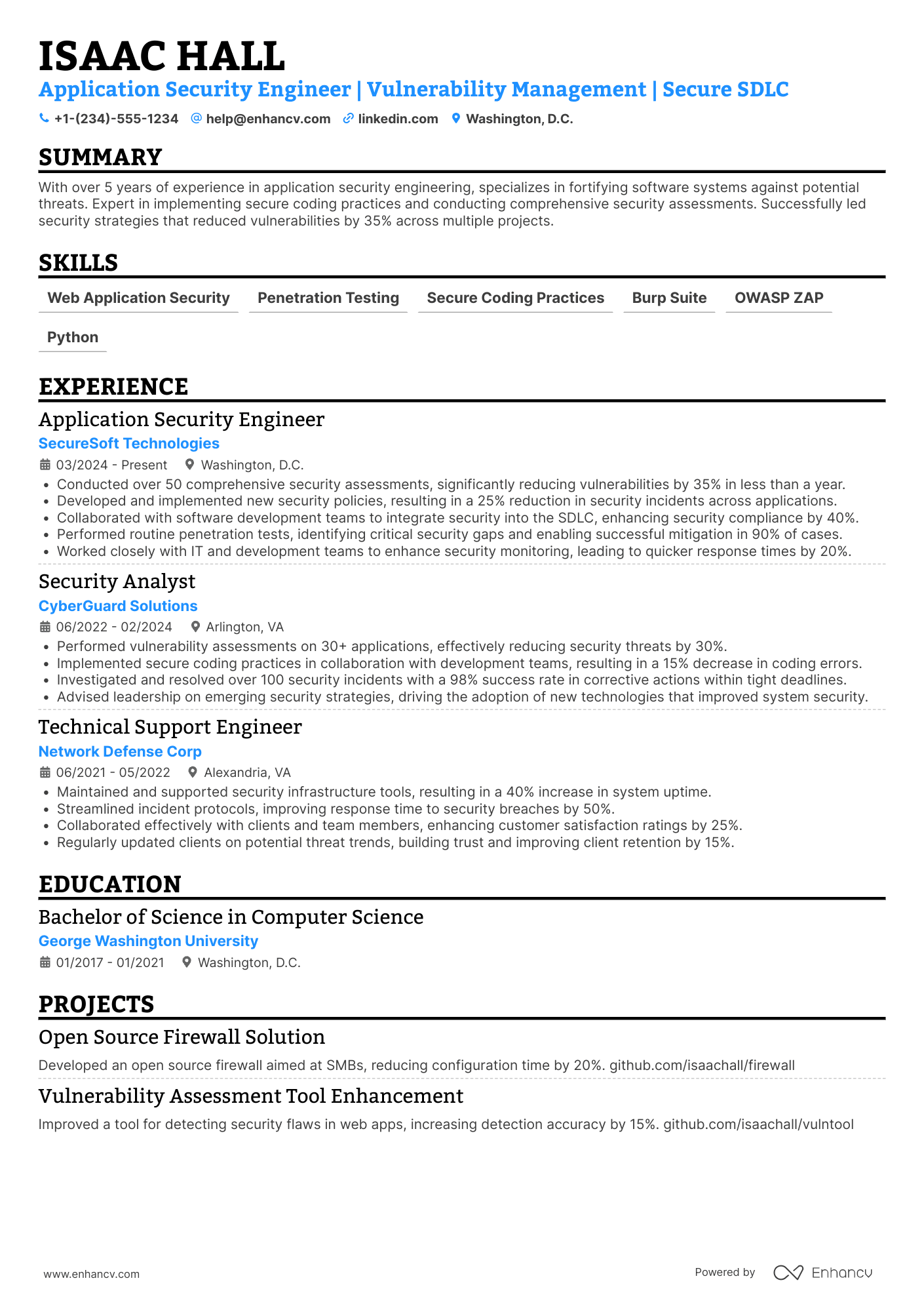
A application security engineer experience example
✅ Right example - modern, quantified, specific.
Application Security Engineer
FinchPay | Remote
2022–Present
Supported a cloud-native payments platform processing over five million transactions per day across North America.
- Implemented a Shift Left program by integrating Semgrep, Snyk, and CodeQL into GitHub Actions, cutting critical vulnerabilities reaching production by 62% and reducing mean time to remediate from twelve days to five days.
- Led threat modeling for eight high-risk features using STRIDE and data flow diagrams, partnering with product managers, designers, and engineers to close forty-three abuse cases before launch and prevent an estimated $900K in annual fraud exposure.
- Built and tuned a dynamic application security testing pipeline with OWASP ZAP and Burp Suite Enterprise, increasing coverage from 35% to 78% of authenticated flows and removing 210 hours per quarter of manual regression testing.
- Hardened application and infrastructure secrets handling by migrating teams to HashiCorp Vault and enforcing OpenID Connect-based short-lived tokens, reducing secret leaks to zero and lowering unauthorized access alerts by 41%.
- Coordinated quarterly penetration tests with an external firm and internal stakeholders, delivering fix plans in Jira and verifying patches in staging, achieving a 96% on-time remediation rate for high-severity findings.
Now that you've seen how a strong experience section comes together, let's look at how to adjust yours to match the specific role you're targeting.
How to tailor your application security engineer resume experience
Recruiters evaluate your application security engineer resume through both manual review and applicant tracking systems. Tailoring your resume to the job description ensures your qualifications register with both.
Ways to tailor your application security engineer experience:
- Match specific SAST and DAST tools listed in the job description.
- Use the exact compliance framework names like SOC 2 or PCI DSS.
- Mirror secure SDLC terminology the employer uses in their posting.
- Highlight threat modeling methodologies referenced in the role requirements.
- Include cloud platform experience when the posting specifies AWS or Azure.
- Reflect DevSecOps pipeline integration if the job description mentions it.
- Emphasize OWASP standards when the employer references application security benchmarks.
- Align vulnerability remediation metrics with the success criteria they describe.
Tailoring means aligning your real accomplishments with what the employer prioritizes—not forcing keywords where they don't belong.
Resume tailoring examples for application security engineer
| Job description excerpt | Untailored | Tailored |
|---|---|---|
| Perform threat modeling and secure code reviews across microservices using OWASP methodologies; integrate SAST/DAST tools into CI/CD pipelines | Reviewed code for security issues and helped improve development processes. | Conducted threat modeling and secure code reviews for 40+ microservices using OWASP ASVS, and integrated Checkmarx (SAST) and OWASP ZAP (DAST) into Jenkins CI/CD pipelines, reducing production vulnerabilities by 55% over two quarters. |
| Partner with engineering teams to remediate vulnerabilities identified through bug bounty and penetration testing programs; track findings in Jira and report metrics to leadership | Worked with developers to fix security bugs and tracked progress on issues. | Partnered with six engineering squads to triage and remediate 120+ vulnerabilities from HackerOne bug bounty and annual penetration tests, tracking remediation SLAs in Jira and delivering monthly executive dashboards that cut mean-time-to-fix from 34 days to 12. |
| Design and deliver secure SDLC training for developers; champion adoption of secrets management and dependency scanning in cloud-native applications on AWS | Provided security training to team members and supported cloud security initiatives. | Designed a secure SDLC training program completed by 200+ developers, increasing secure coding assessment scores by 30%, while driving org-wide adoption of HashiCorp Vault for secrets management and Snyk for dependency scanning across 15 AWS-hosted cloud-native services. |
Once your experience aligns with the role’s priorities, the next step is to quantify your application security engineer achievements to show the impact of that work.
How to quantify your application security engineer achievements
Quantifying your achievements proves your security work changed outcomes, not just processes. Focus on risk reduction, vulnerability closure speed, secure release cadence, incident prevention, and engineering efficiency using measurable results from scans, pipelines, and production.
Quantifying examples for application security engineer
| Metric | Example |
|---|---|
| Risk reduction | "Reduced critical production vulnerabilities by 62% in two quarters by enforcing SAST (Semgrep) and SCA (Snyk) gates on 140 repositories." |
| Delivery speed | "Cut security review turnaround from five days to one day by shipping a threat modeling template and automating Jira intake for 30 teams." |
| Detection quality | "Lowered false positives by 45% by tuning CodeQL queries and adding suppression rules, saving 120 engineer hours per month." |
| Incident prevention | "Prevented three high-severity injection paths by adding GraphQL input validation and WAF rules, dropping related alerts from 40 per week to six." |
| Cost efficiency | "Reduced third-party security tool spend by $85,000 annually by consolidating scanners and negotiating enterprise licensing across 1,200 developers." |
Turn vague job duties into measurable, recruiter-ready resume bullets in seconds with Enhancv's Bullet Point Generator.
Once you've crafted strong bullet points for your experience section, you'll want to apply that same precision to presenting your hard and soft skills effectively.
How to list your hard and soft skills on a application security engineer resume
Your skills section shows you can secure software across the development lifecycle, and recruiters and an ATS (applicant tracking system) scan this section to match job keywords—aim for mostly hard skills with a smaller set of role-specific soft skills. application security engineer roles require a blend of:
- Product strategy and discovery skills.
- Data, analytics, and experimentation skills.
- Delivery, execution, and go-to-market discipline.
- Soft skills.
Your skills section should be:
- Scannable (bullet-style grouping).
- Relevant to the job post.
- Backed by proof in experience bullets.
- Updated with current tools.
Place your skills section:
- Above experience if you're junior or switching careers.
- Below experience if you're mid/senior with strong achievements.
Hard skills
- Secure SDLC, threat modeling
- OWASP Top 10, ASVS
- SAST: Semgrep, CodeQL
- SCA: Snyk, Dependabot
- DAST: Burp Suite, OWASP ZAP
- API security testing: Postman, Burp
- Secure code review: Java, Python
- CI/CD security: GitHub Actions, Jenkins
- Container security: Docker, Trivy
- IaC security: Terraform, Checkov
- Cloud security: AWS, IAM
- Secrets management: Vault, KMS
Soft skills
- Translate risk into impact
- Write clear remediation guidance
- Partner with developers in reviews
- Negotiate security tradeoffs
- Prioritize by exploitability and reach
- Run blameless incident follow-ups
- Drive fixes to closure
- Communicate in threat-model sessions
- Align security with delivery timelines
- Influence standards without blocking teams
- Document decisions and exceptions
- Escalate issues with crisp context
How to show your application security engineer skills in context
Skills shouldn't live only in a dedicated skills list. Browse resume skills examples to see how top candidates weave competencies throughout their documents.
They should be demonstrated in:
- Your summary (high-level professional identity)
- Your experience (proof through outcomes)
Here's what strong, contextual skill placement looks like in practice.
Summary example
Senior application security engineer with eight years of experience securing fintech platforms. Skilled in threat modeling, SAST/DAST tooling, and secure SDLC integration. Led enterprise-wide OWASP Top 10 remediation, reducing critical vulnerabilities by 74% across 12 microservices.
- Signals senior-level depth immediately
- Names specific tools and frameworks
- Leads with a measurable outcome
- Shows cross-team leadership ability
Experience example
Senior Application Security Engineer
Vantage Financial Technologies | Remote
March 2020–Present
- Integrated Checkmarx and Burp Suite into CI/CD pipelines, cutting mean vulnerability remediation time from 18 days to five across 30 repositories.
- Partnered with platform engineering to design a secure API gateway, eliminating 90% of injection-related incidents within six months.
- Led quarterly threat modeling workshops for 40 developers, improving secure coding adoption rates by 63% year over year.
- Every bullet includes measurable proof
- Skills surface naturally through achievements
Once you’ve tied your security work to real outcomes and responsibilities, the next step is applying that same approach to building an application security engineer resume with no experience.
How do I write a application security engineer resume with no experience
Even without full-time experience, you can demonstrate readiness through projects and hands-on practice. Our guide on writing a resume without work experience covers the core strategies in detail. Here are strong options for application security engineer candidates:
- Capture-the-flag web security challenges
- Bug bounty reports and write-ups
- Open-source security pull requests
- Secure code review practice repos
- OWASP Top Ten lab projects
- Threat modeling for sample apps
- Static analysis tool baselining
- Security-focused hackathon submissions
Focus on:
- Secure coding and code review
- OWASP Top Ten remediation evidence
- Tool output turned into fixes
- Measurable risk reduction results
Resume format tip for entry-level application security engineer
Use a hybrid resume format because it highlights projects and technical skills first, while still showing a clean timeline for education and work. Do:
- Lead with a projects section.
- Name tools you used and why.
- Quantify findings, fixes, and coverage.
- Link to repositories and write-ups.
- Map work to OWASP Top Ten.
- Built an OWASP Juice Shop lab pipeline using Semgrep and OWASP ZAP, found twelve issues, and fixed nine, cutting high-severity findings by 75%.
When you're building your resume without direct experience, your education section becomes one of the strongest tools for demonstrating relevant knowledge and qualifications.
How to list your education on a application security engineer resume
Your education section helps hiring teams confirm you have the foundational knowledge needed for an application security engineer role. It validates technical training and academic rigor quickly.
Include:
- Degree name
- Institution
- Location
- Graduation year
- Relevant coursework (for juniors or entry-level candidates)
- Honors & GPA (if 3.5 or higher)
Skip month and day details—list the graduation year only.
Here's a strong education entry tailored for an application security engineer resume.
Example education entry
Bachelor of Science in Computer Science
Georgia Institute of Technology, Atlanta, GA
Graduated 2021
GPA: 3.7/4.0
- Relevant Coursework: Network Security, Secure Software Development, Cryptography, Operating Systems, and Ethical Hacking
- Honors: Dean's List (six semesters), Magna Cum Laude
How to list your certifications on a application security engineer resume
Certifications on your resume show your commitment to learning, prove tool proficiency, and signal industry relevance for an application security engineer across modern development and cloud environments. Include:
- Certificate name
- Issuing organization
- Year
- Optional: credential ID or URL
- Place certifications below education when they're older, less relevant to application security engineer work, or when your degree is your strongest, most recent credential.
- Place certifications above education when they're recent, highly relevant to application security engineer duties, or required by the roles you're targeting.
Best certifications for your application security engineer resume
- Offensive Security Certified Professional (OSCP)
- GIAC Web Application Penetration Tester (GWAPT)
- Certified Information Systems Security Professional (CISSP)
- Certified Cloud Security Professional (CCSP)
- Certified Secure Software Lifecycle Professional (CSSLP)
- Burp Suite Certified Practitioner
Once you’ve positioned your credentials where recruiters will notice them, move on to your application security engineer resume summary to frame those qualifications in a clear, role-relevant snapshot.
How to write your application security engineer resume summary
Your resume summary is the first thing a recruiter reads. A strong one immediately signals you have the right skills and experience for an application security engineer role.
Keep it to three to four lines, with:
- Your title and relevant years of experience in application security.
- The domain or industry you've worked in, such as fintech, SaaS, or e-commerce.
- Core tools and skills like SAST, DAST, threat modeling, OWASP, or secure SDLC.
- One or two quantified achievements that show your real-world impact.
- Soft skills tied to outcomes, such as cross-team collaboration that reduced remediation time.
PRO TIP
At this level, focus on specific tools you've used and measurable contributions, even small ones. Highlight relevant certifications, coursework, or internship work that shows hands-on ability. Avoid vague phrases like "passionate about security" or "fast learner." Replace them with concrete skills and results recruiters can verify.
Example summary for a application security engineer
Application security engineer with two years of experience securing SaaS platforms. Reduced critical vulnerabilities by 40% using SAST and DAST tools. Collaborated with developers to integrate threat modeling into CI/CD pipelines.
Optimize your resume summary and objective for ATS
Drop your resume here or choose a file.
PDF & DOCX only. Max 2MB file size.
Now that your summary captures your security expertise at a glance, make sure your header provides the essential contact and professional details recruiters need to reach you.
What to include in a application security engineer resume header
A resume header lists your key identifiers and contact details, improving visibility, credibility, and recruiter screening for a application security engineer role.
Essential resume header elements
- Full name
- Tailored job title and headline
- Location
- Phone number
- Professional email
- GitHub link
- Portfolio link
A LinkedIn link helps recruiters confirm your work history fast and supports quick screening decisions.
Do not include a photo on a application security engineer resume unless the role is explicitly front-facing or appearance-dependent.
Keep your header consistent with your application security engineer focus by matching your headline to the job posting and using links that load quickly.
Example
Application security engineer resume header
Jordan Lee
Application security engineer | Web app security, secure code review, threat modeling
Austin, TX
(512) 555-01XX
your.name@enhancv.com
github.com/yourname
yourwebsite.com
linkedin.com/in/yourname
Once your contact details, role focus, and key credentials are clear at the top, add targeted additional sections to provide supporting context without crowding the header.
Additional sections for application security engineer resumes
When your core sections don't fully capture your expertise, additional sections help you stand out and reinforce your application security engineer credibility.
- Security certifications and training
- Published vulnerability research and CVE disclosures
- Open-source security tool contributions
- Conference talks and presentations
- Languages
- Bug bounty achievements and recognitions
- Professional memberships and affiliations
Once you've strengthened your resume with relevant additional sections, pairing it with a well-crafted cover letter can further set your application apart.
Do application security engineer resumes need a cover letter
A cover letter isn't required for an application security engineer, but it helps in competitive searches and teams with strict hiring expectations. Understanding what a cover letter is and when to use one can make a difference when your resume needs context, or when the role demands close product and engineering alignment.
Use a cover letter to add context your resume can't:
- Explain role and team fit by mapping your strengths to the team's stack, SDLC, and security program maturity.
- Highlight one or two relevant projects or outcomes, including the risk reduced, vulnerabilities prevented, or delivery friction removed.
- Show understanding of the product, users, or business context by tying security work to reliability, trust, and release cadence.
- Address career transitions or non-obvious experience by connecting past work to threat modeling, secure code review, or developer enablement.
Drop your resume here or choose a file.
PDF & DOCX only. Max 2MB file size.
If you decide a cover letter won’t add value, using AI to improve your application security engineer resume helps you strengthen your core document and tailor it faster.
Using AI to improve your application security engineer resume
AI can sharpen your resume's clarity, structure, and impact. It helps you refine bullet points, tighten language, and align content with real job demands. But overuse kills authenticity. Once your resume is clear and role-aligned, step away from AI entirely. For practical starting points, explore these ChatGPT resume writing prompts tailored to different resume sections.
Here are 10 practical prompts you can copy and paste to strengthen specific sections of your application security engineer resume:
Strengthen your summary
Quantify experience bullets
Align skills to job posts
Sharpen project descriptions
Improve action verbs
Tighten certification entries
Refine education details
Remove filler language
Tailor for ATS systems
Clarify technical scope
Conclusion
A strong application security engineer resume shows measurable outcomes, role-specific skills, and a clean structure. Highlight reduced vulnerabilities, faster remediation, and fewer production issues. Keep sections scannable, and align your experience with secure coding, threat modeling, and code review.
Hiring teams want application security engineer candidates who can protect modern stacks and ship safely. Use clear metrics, targeted keywords, and consistent formatting to show impact and readiness. When your results and skills are easy to find, interviews follow.